How Governments and Authorities Restrict Access to the Internet
The number of Internet censorship cases has increased throughout the world since 2010 onwards, especially beginning with the Arab Spring uprisings of early 2011. And according to the latest Freedom on the Net 2020 report from Freedom House, the COVID-19 pandemic was another catalyst for this, fueling digital repression in 2020:
“Global internet freedom has declined for the 10th consecutive year: 26 countries’ scores worsened during this year’s coverage period, while 22 countries registered net gains.”
According to the report cited above, the largest declines in internet freedom occurred in Myanmar and Kyrgyzstan, followed by India, Ecuador, and Nigeria. A record number of countries featured deliberate disruptions to internet service. Myanmar in particular saw an even worse turn just at the beginning of 2021, when the military coup affected internet connectivity throughout the country.
The motivations for internet censorship are diverse, but can be split into 3 main purpose categories: political stability, traditional social values and national security. But how exactly does this happen from a technical standpoint? This article will hopefully shed some more light on how governments / authorities censor the internet.
Why Speedify VPN Stays Connected in Under a Second When Other VPNs Drop
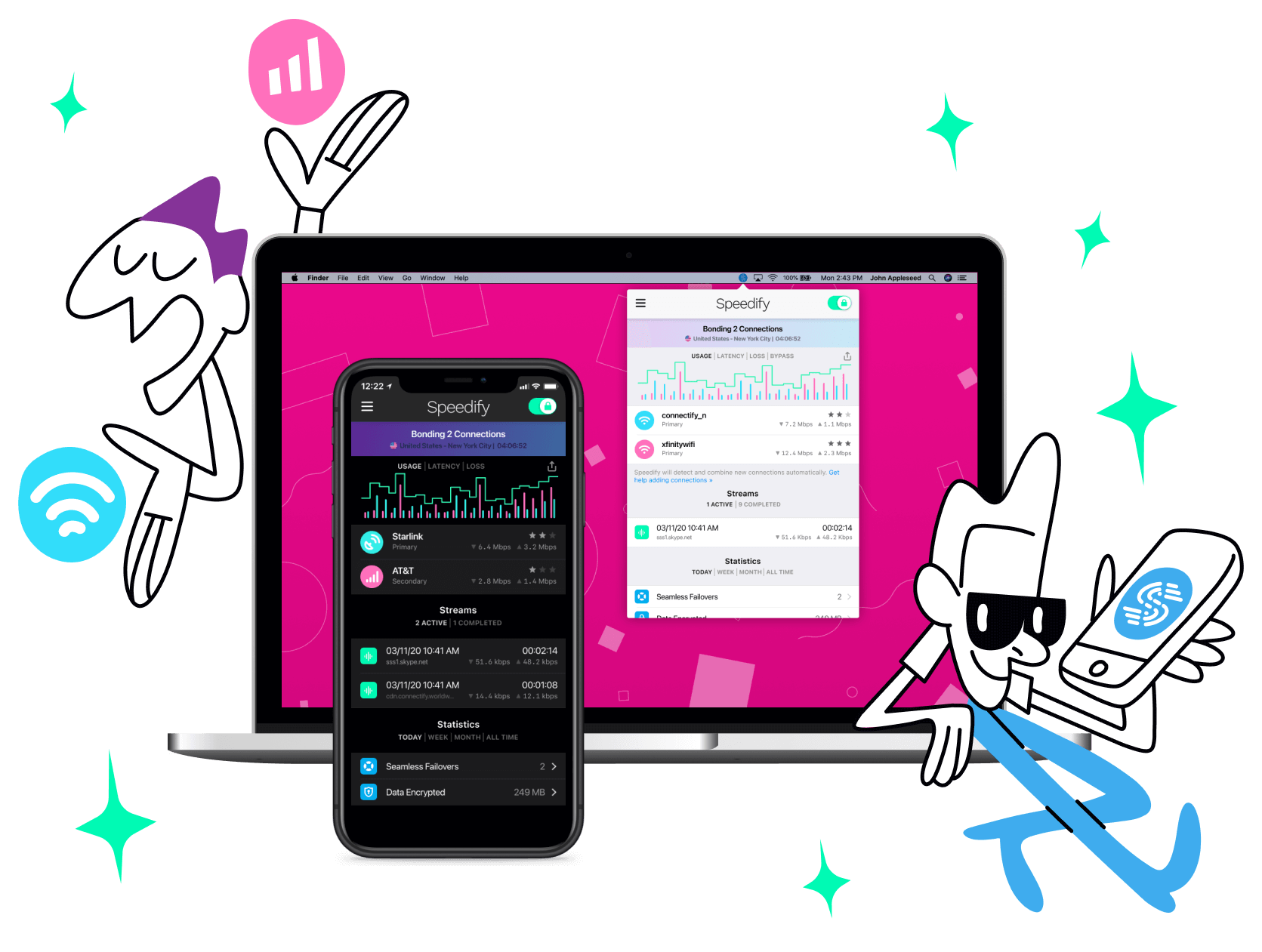
Most VPNs rely on a single internet connection. If your Wi-Fi glitches or your device switches between 4G/5G cellular and Starlink, your VPN drops.
Speedify uses all your available internet connections at the same time: Wi-Fi, 4G/5G cellular, Ethernet, Starlink, and other satellites. If one drops, Speedify detects it within milliseconds and moves your traffic to another available internet connection. Traditional routers take 30–60 seconds to do the same thing.
In this video, you’ll see how Speedify keeps your internet connection secure, smooth, and reliable by intelligently spreading your encrypted data across Wi-Fi, 4G / 5G cellular, Ethernet, Starlink and other satellites. The result: an unbreakable VPN tunnel.
Combining Wi-Fi, 4G / 5G Cellular, Ethernet, Starlink and Other Satellites Together Makes Speedify VPN Unbreakable
Speedify combines 5G, 4G, Wi-Fi, Ethernet, Starlink and other satellite into one secure and unbreakable VPN tunnel
Speedify is the only VPN app that seamlessly combines Wi-Fi, 4G / 5G cellular, Ethernet, Starlink and other satellite internet into one unbreakable internet connection. You get faster upload and download speeds while no one can spy on what you do online. Speedify allows you to unblock restricted content by connecting to one of the VPN servers distributed across 6 continents in 50+ cities.
Speedify will automatically detect any available Internet connections on your device, encrypting and intelligently distributing your online traffic between them for optimal performance. If you need help we have quick start guides available for most common set ups.
Speedify combines multiple personal hotspots for faster internet upload and download speeds
Speedify's Pair & Share feature enables you to connect to multiple hotspots at the same time for faster upload and download speeds and more reliable internet for everyone. Speedify's Pair & Share feature allows you to wirelessly share 4G / 5G cellular connections back and forth between multiple Speedify users on the same local network when live streaming from an event, calling from the commute or sharing from the field.
Speedify is the only app that allows you to share cellular data between PCs, Macs, iPhones and Androids. Use multiple iPhones and Android phones as hotspots for internet access and get faster upload and download speeds and mobile failover for all paired devices.
See how you can use Speedify to combine available Internet connections:
Combine these connections on:
The Basics: How Internet Works
Before understanding how they censor the internet, you need to understand how the internet works and what are the levers to pull for this purpose. We’ll use an oversimplified example of you accessing a website on a computer over the free internet. Here are the elements involved:
- Your Internet Service Provider (ISP) - you use them to connect to the internet. Comcast, Verizon, AT&T, Vodafone - these are examples of ISPs. Their role is to provide internet connectivity to their customers through their infrastructure consisting of online servers, connections and networking equipment.
- Your Internet Protocol (IP) address - this is unique, like a postal address, assigned to you by your ISP. It is used to identify you and move information. Websites have IP addresses as well.
- The Domain Name System (DNS) - allows IP addresses to be associated with human-readable “domain names” such as speedify.com.
- Numbered Ports are used within internet protocols for specific purposes. Each port can be assigned to a particular activity - e.g. the default port for browsing is 80.
- The Gateways are a kind of large scale routers that allow ISPs to connect to the internet backbone, thus being able to communicate with each other.
- Network packets are the basic elements that form a flow of information. They are formatted units of data carried over the Internet.
Going back to our example - here’s what happens when you type in “https://speedify.com”:
- Your computer sends the domain name request "speedify.com" to a selected DNS server, which resolves it, returning a message containing the IP address for the server that hosts the Speedify website.
- The browser sends a request to your ISP for a connection to that IP address.
- The request goes through a series of routers, each one forwarding a copy of the request to a router closer to the destination, until it reaches a router that finds the specific computer needed - the one that hosts the Speedify website.
Each such router along a path can be referred to as a "hop"; the number of hops is the number of computers or routers your message comes in contact with along its way and is often between 5 and 30. - This computer sends information back to you, allowing your browser to send the full URL and receive the data to display the Speedify web page.
Internet Censorship: How They Do It
Internet censorship can manifest itself in various forms. These include:
- Filtering content - users can access the website or the app, but that may be missing elements. For example - videos or embedded social media posts on websites, articles that include specific terms, etc.
- Throttling the speed to specific content - for example streaming media.
- Restricting access to content - only specific users can access certain content.
- Blocking content - users cannot access the website or use the app at all.
- Shutting down the internet altogether.
Let’s assume you want to access https://speedify.com from a country where it has been restricted. Here are the most common used technical strategies to prevent online information from reaching users. These techniques don’t just apply to browsing, but to apps, file transfers and all other Internet activities.
DNS filtering and redirection
This assumes that authorities have control over the domain name servers. The government can choose to eliminate specific domains from the DNS server, making them “invisible” to those trying to access them through those DNS servers. They can also replace the original domain with a specific one.
When you type in our website’s address, the browser won’t return anything. Or, it can redirect you to a predefined website imposed by your government.
IP address blocking
This assumes that authorities have control over ISPs. They can blacklist certain IP addresses of websites they want to block. When you request access to a site, your request is monitored by surveillance computers, which check your request against a list of blacklisted IP addresses. Trying to reach speedify.com, which in our example is blocked? The internet service provider will drop the connection, causing it to fail.
URL filtering
In this case, the URL (Uniform Resource Locator) or web address is scanned by the surveillance computers for specific keywords. If those are found, the connection will be restricted.
So, if your government doesn’t want you to use Facebook, and you’re trying to access our blog on Facebook streaming at https://speedify.com/blog/better-streaming/livestream-event-facebook/, then you won’t be able to access it.
Packet filtering
This assumes that authorities scan the contents of each network packet sent to and from your computer. By using deep packet inspection technologies, they examine packet contents for banned keywords. Communication identified as containing forbidden content can be disrupted by dropping the connection. You may receive an error message in your browser, none indicating explicitly that you are being censored.
As in the example above, when you’re trying to access the page about Facebook, you will not succeed.
Outside of these, there are a plethora of other technologies for censoring the internet - check out these great resources from Townsend Center and Wikipedia.
How to Circumvent Internet Censorship
There are several possibilities to bypass restrictions on content online. Let’s go through the main ones.
HTTPS
Hypertext Transfer Protocol Secure (HTTPS) is basically a secure version of the HTTP protocol (HTTP over TLS), where nobody can see the data you send and receive from the internet, while it moves between your device and the destination server. It protects against man-in-the-middle attacks, eavesdropping and network tampering.
If the website you’re trying to access uses HTTPS, then you have a better chance that it will work and that the contents of your page won't be filtered or modified. However, the domain name is still left unencrypted, so, if authorities filter that domain name, this won’t work.
DNS over HTTPS (DoH)
This protocol is useful in circumventing internet censorship as it can eliminate DNS restrictions from governments. All the processes involved in requesting, finding and sending back the domain server name are encrypted over the HTTPS protocol.
In order to use this, you need an application that has built-in DoH implementation (such as a web browser, operating systems, etc.).
The downside of this is that in many cases not all the elements of the connection are encrypted, leaving room for authorities to restrict the traffic.
Encrypted Server Name Indication (ESNI) and Encrypted Client Hello (ECH)
These are both related protocol extensions for TLS; it all started in 2018 with ESNI and continued in 2020 with ECH. What ECH basically does is secure the meta data left unencrypted by HTTPS, including the server name. This makes ECH one of the best protocol choices for circumventing restrictions, to be included by ISPs, apps, developers, etc.
However, it’s not 100% proof to censorship. For example, the length of that encrypted negotiation between servers may leak enough information about the domain name, to be guessed.
Virtual Private Networks (VPN)
Out of several possibilities to bypass restricted internet content, using a virtual private network (VPN) is the easiest way to go at it. All you need to do is use it when you want to access a blocked resource. Naturally, this assumes that the VPN’s server IP addresses aren’t blocked by the authorities.
A VPN encrypts all communication between your computer and a server in the cloud. This way, nobody can monitor or inspect what you’re accessing online. The only thing they will see is you connecting to a specific IP.
When you’re choosing your VPN, make sure to get one that doesn’t slow down your Internet. You can look at bonding VPNs like Speedify, for example, which allow you to combine all of your internet connections at once right on your computer or mobile device. You’ll get faster, more reliable and secure Internet.
Speedify uses advanced encryption to send and receive data from its network of hundreds of servers worldwide. We believe in the freedom of the internet, so that’s why we are supporting users everywhere there is Internet censorship. Take Myanmar for example.
If you live in a country where there is Internet censorship, you should definitely try using a VPN like Speedify. Get it now and enjoy free data on us!
Get started with Speedify today!
With Speedify you can combine Wi-Fi, 4G / 5G cellular, Ethernet, Starlink and other satellites into one bonded super-connection to improve livestreaming, video calling, gaming, web browsing, and everything else you do online.
Speed
Stability
Security
Speedify engineers love talking tech on YouTube, Tiktok, and Instagram!
Alex Gizis and the Speedify engineers discuss and explain technology including Starlink satellites, Wi-Fi 7 routers, Apple networking features, fiber optics, broadband internet, 5G mobile networks, AI, networking protocols, and much more. Follow Speedify on YouTube, TikTok, Instagram, and LinkedIn!
Alex and the Speedify team are always exploring the latest in networking and security technology—like 5G, 6G, WiFi 7, laser and satellite internet—and sharing it in new discussion content across YouTube, TikTok, Instagram, and LinkedIn every week.
Got a tech question? Let's go deeper! Pop into Speedify Office Hours live every Wednesday at 10 AM Eastern. Speedify CEO Alex Gizis and our network engineers are standing by to break down your questions about networks, tech updates, and Speedify features.